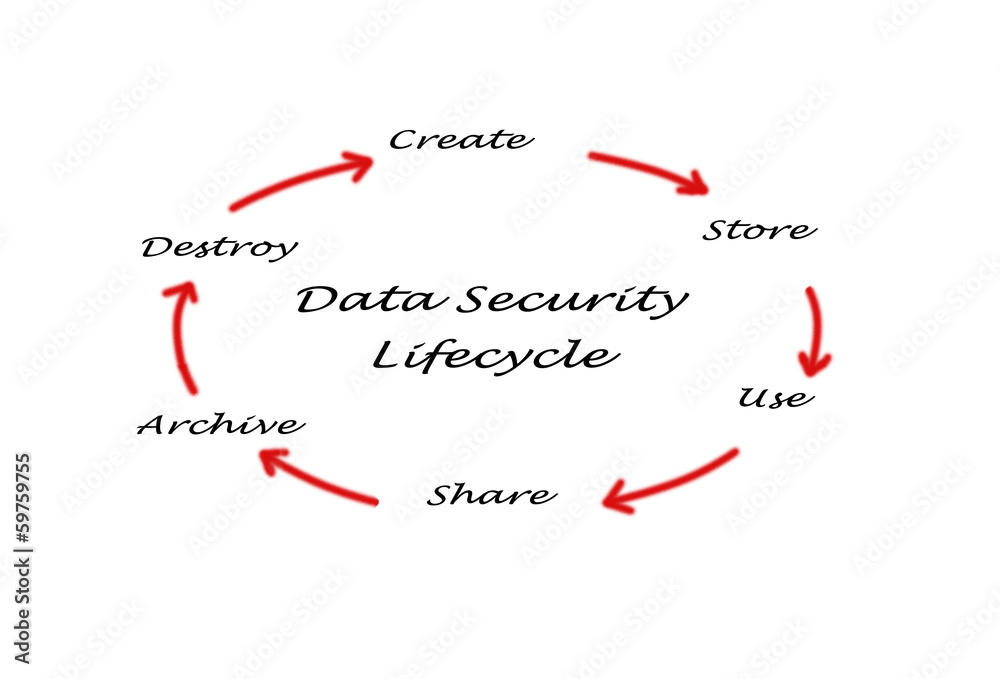
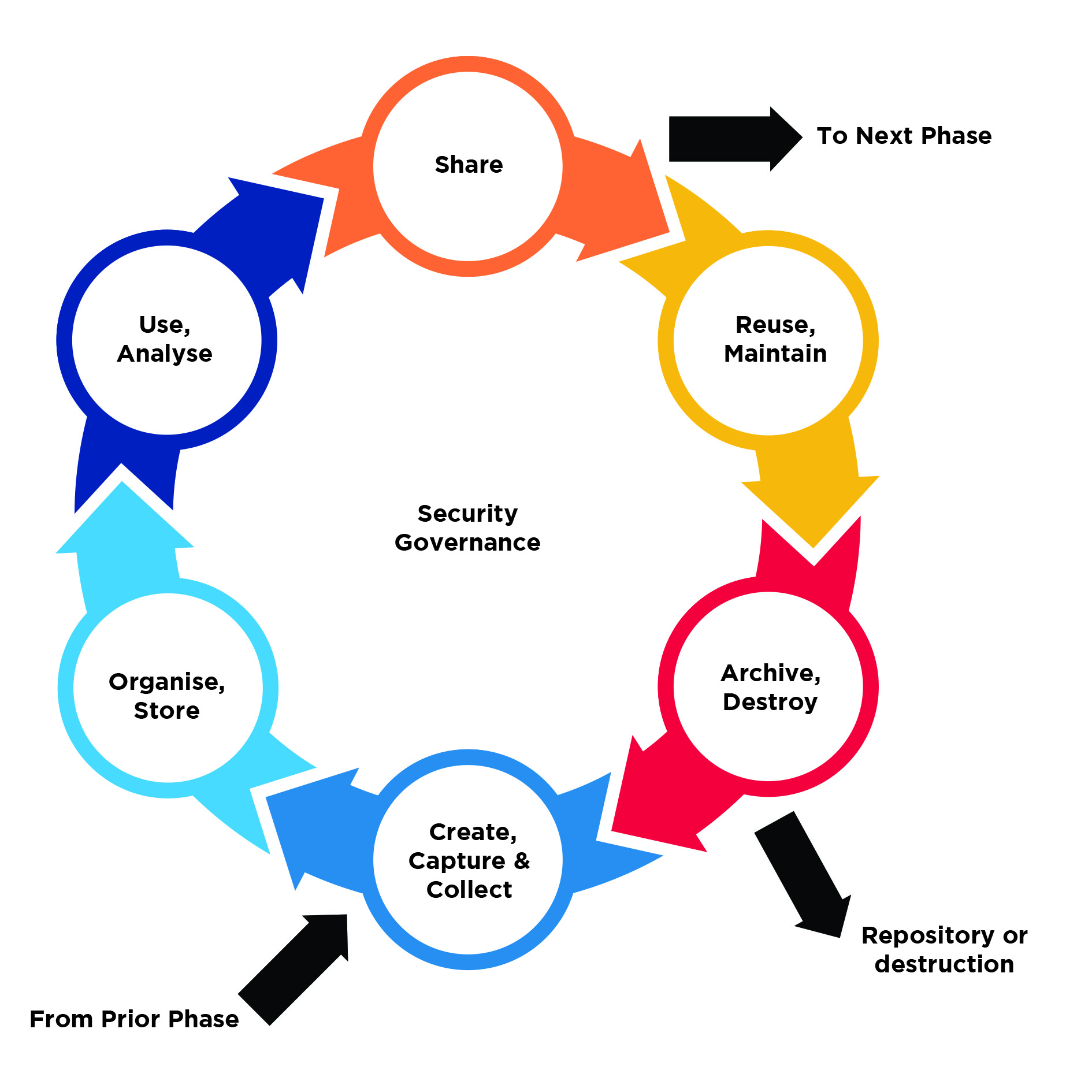
Master Your Data Lifecycle to Improve Data Security - Enterprise Network Security Blog from IS Decisions
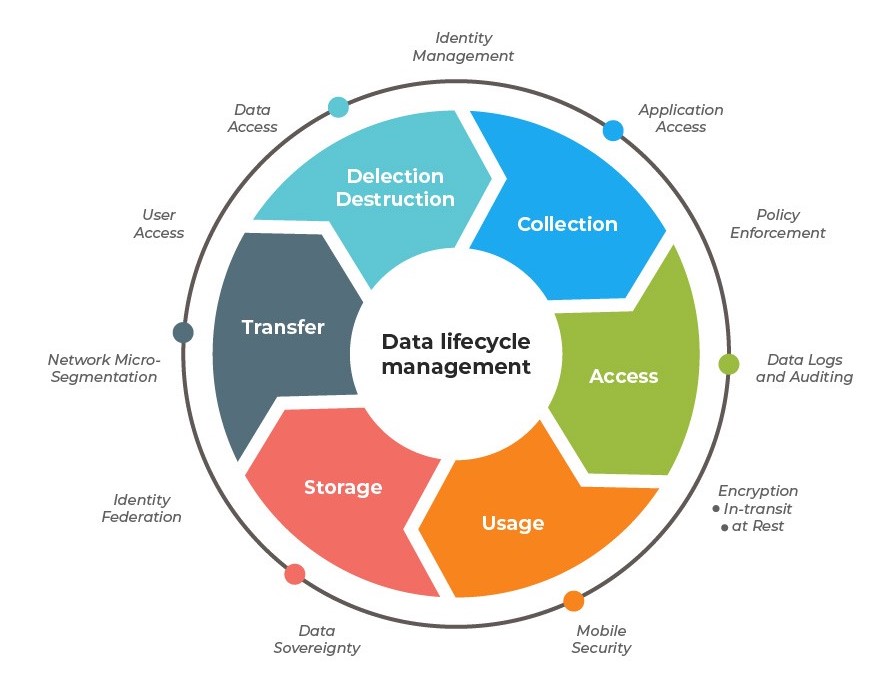
Data lifecycle management (DLM) - a solution to increase an efficiency in data management according to the Person Data Protection Act (PDPA) - ADD+ Leader in IT Asset Disposal in Asia