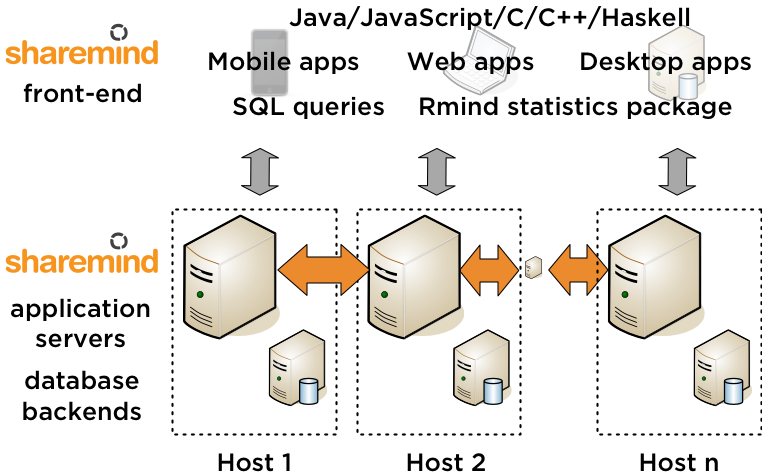
![PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/54858338e517a3112133e7e664d762299842671b/5-Figure2-1.png)
PDF] Secure Multiparty Computation during Privacy Preserving Data Mining: Inscrutability Aided Protocol for Indian Healthcare Sector | Semantic Scholar
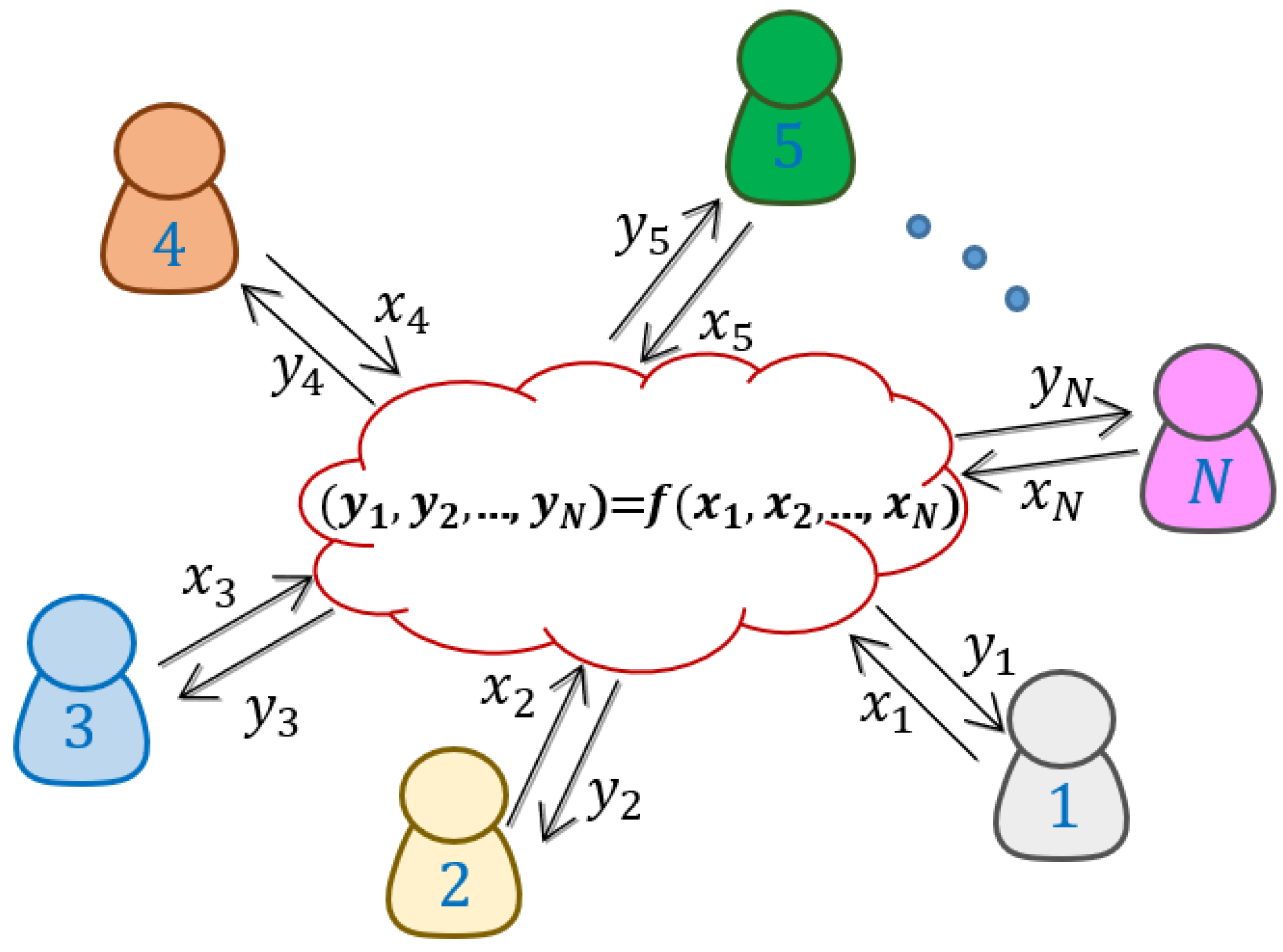
1 Privacy Preserving Data Mining Haiqin Yang Extracted from a ppt “Secure Multiparty Computation and Privacy” Added “Privacy Preserving SVM” - ppt download
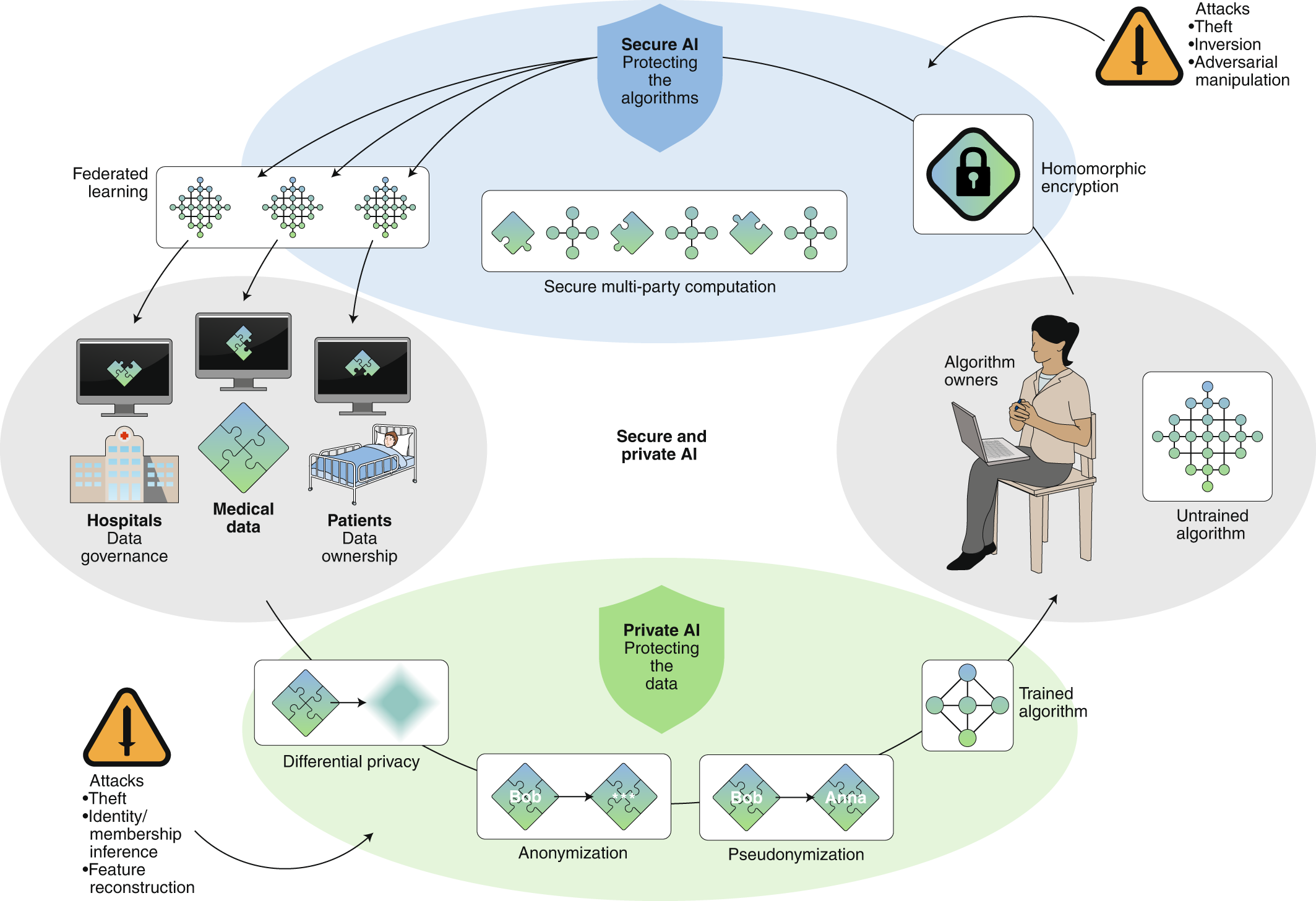
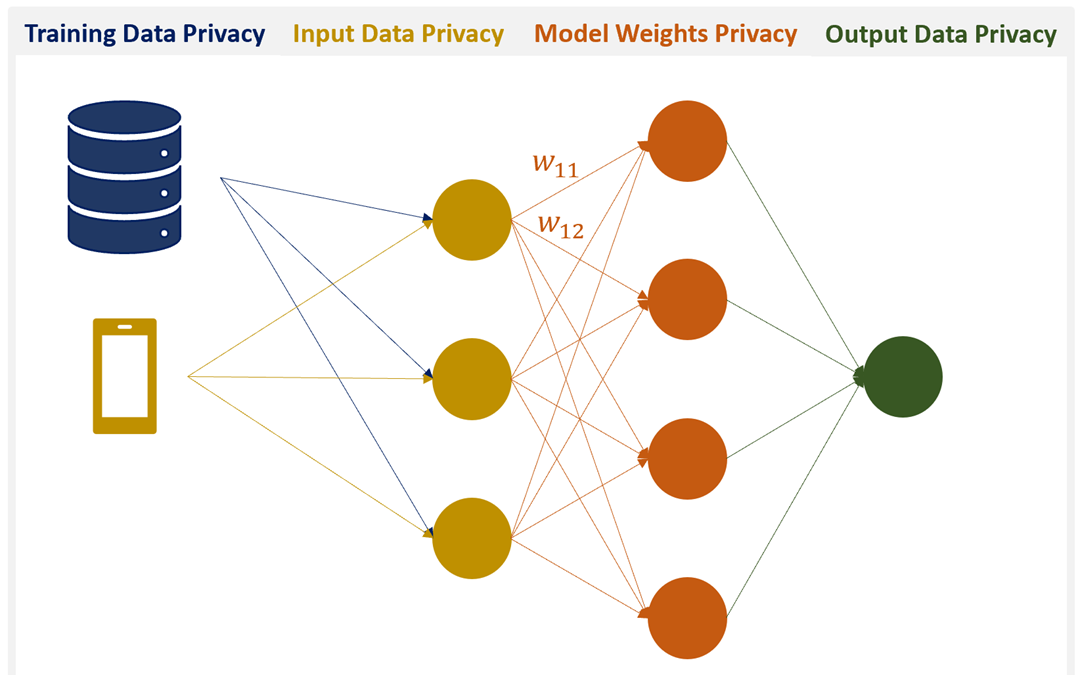
Secure, privacy-preserving and federated machine learning in medical imaging | Nature Machine Intelligence

PDF) Fostering the Uptake of Secure Multiparty Computation in E-Commerce | Octavian Catrina and Octavian Catrina - Academia.edu
Perfectly Privacy-Preserving AI. What is it and how do we achieve it? | by Patricia Thaine | Towards Data Science
Applied Sciences | Free Full-Text | Generation and Distribution of Quantum Oblivious Keys for Secure Multiparty Computation
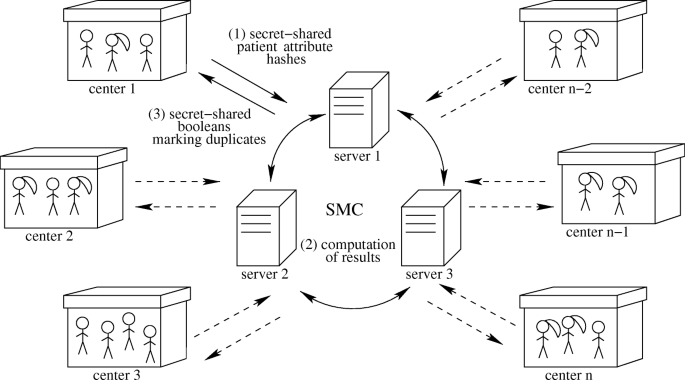
Privacy-preserving record linkage in large databases using secure multiparty computation | BMC Medical Genomics | Full Text
![PDF] Secure Multiparty Computation for Privacy-Preserving Data Mining | Semantic Scholar PDF] Secure Multiparty Computation for Privacy-Preserving Data Mining | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/55682d5db7f02b99ee979c3cda256b5db494c6fb/2-Figure1-1.png)