Challenges and Developments in Secure Routing Protocols for Healthcare in WBAN: A Comparative Analysis | Wireless Personal Communications
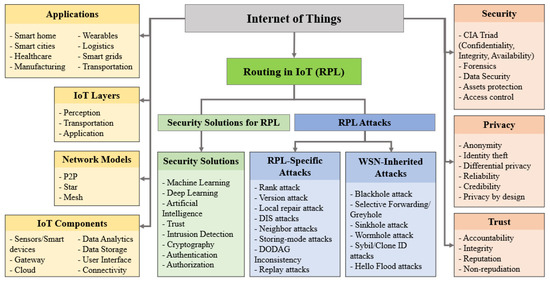
Sensors | Free Full-Text | Trust and Mobility-Based Protocol for Secure Routing in Internet of Things

RETRACTED ARTICLE:An optimized distributed secure routing protocol using dynamic rate aware classified key for improving network security in wireless sensor network | Journal of Ambient Intelligence and Humanized Computing

Trust-based secure routing and message delivery protocol for signal processing attacks in IoT applications | The Journal of Supercomputing

Secure Multipath Routing Protocols in Wireless Sensor Networks: A Security Survey Analysis | Semantic Scholar
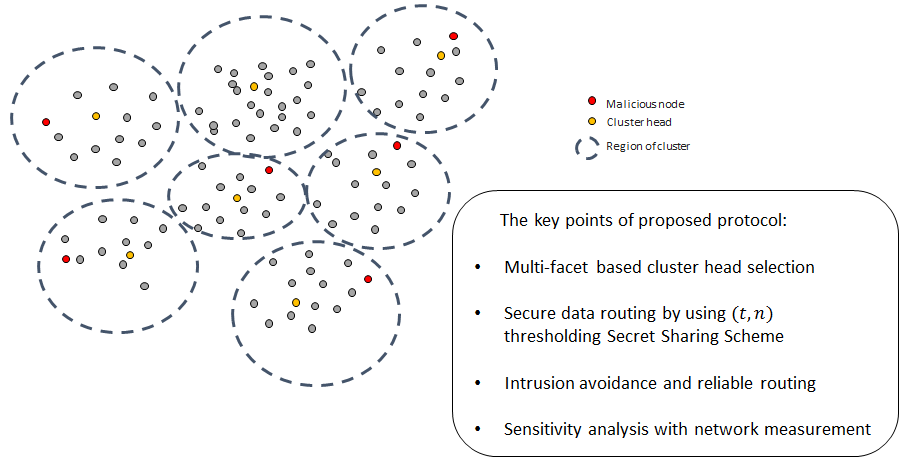
Energies | Free Full-Text | An Energy-Efficient and Secure Routing Protocol for Intrusion Avoidance in IoT-Based WSN
Secure Routing in Ad Hoc Wireless Networks | Transport Layer and Security Protocols for Ad Hoc Wireless Networks | InformIT
File:Secure routing protocol over mobile Internet of Things wireless sensor networks (IA secureroutingpro1094558273).pdf - Wikimedia Commons

Table 4.1 from An Efficient Security Aware Routing Protocol for Mobile Ad Hoc Networks | Semantic Scholar








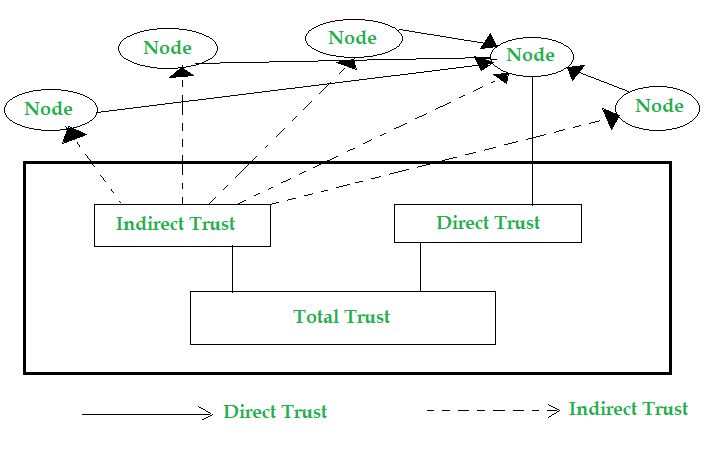
![PDF] A Security-Aware Routing Protocol for Wireless Ad Hoc Networks | Semantic Scholar PDF] A Security-Aware Routing Protocol for Wireless Ad Hoc Networks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4194e46bfc559e52a5389a3dd61ea9c40c90553b/1-Figure1-1.png)